Understanding the Essentials of Pairing Applications
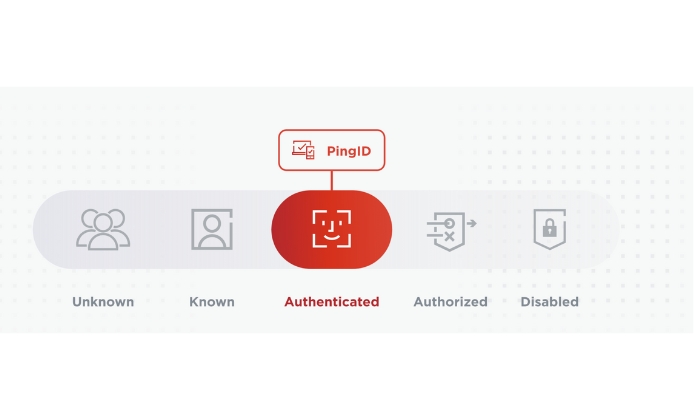
Modern cyber security solutions provide various unique features that make them exceptional tools for enhancing security. One such crucial feature is application pairing, providing a seamless, secure connection between multiple devices. In the midst of all these advanced solutions, the PingID pairing stands out as an essential tool set focused on improving the security framework of an organization.
Detailed Process for Linking Digital Platforms
While discussing multiple device connectivity, it's vital to comprehend the mechanics behind the PingID pairing process. Typically, it concentrates on engaging a secure platform for pairing, driven by a uniquely generated pairing key.
Procedure for Pairing on Desktop
When the conversation gravitates towards pairing related aspects, the PingID pairing desktop version captures significant attention. The desktop version stands out through its user-friendly interface and robust security measures. Notably, the pairing procedure on the desktop is not very different from the mobile application. It promotes a breeze like experience for the users with its simplistic yet effective pairing procedure.
Importance of the Pairing Key
When delving into the essentials of the PingID pairing process, the pairing key capability proves to be a central component. With a PingID pairing key, you ensure that the pairing process remains secure and impenetrable. It serves as an initial assurance that the connection between the devices is genuine and prevents any unauthorized pairing scenarios.
Benefits of Successful Pairing
- Enhanced Security: With a successful pairing, users can rest assured about the security of their online resources.
- Friction-less User Experience: Effective application pairing prevents opportunity for confusion or errors, providing a smooth user experience.
- Accelerated Productivity: With no worry of security breaches, organizations can focus more on their core businesses.



 Enhance Security With Advanced Pairing Feature of PingID App
Enhance Security With Advanced Pairing Feature of PingID App
 Unlock Your Digital World With PingID on iOS Devices
Unlock Your Digital World With PingID on iOS Devices
 Unleashing the Potential of PingID Application
Unleashing the Potential of PingID Application
 An In-Depth Look at PingID: Harnessing Modern Security
An In-Depth Look at PingID: Harnessing Modern Security
